
Automating CloudFormation Deployments with Git sync
Git sync provides remote management of stacks, enabling customers to synchronize their stacks from a CloudFormation template stored in a remote Git repository.
Published Jan 27, 2024
Last Modified Aug 7, 2024
Setting Up Your GitHub Repo
- Hop into GitHub: Just slide into your GitHub account. No account yet? No sweat, signing up is a breeze.
- Dashboard Time: Once you're in, you're gonna land on your dashboard. It's your command center.
- Repo Magic:
- Hit the '+' sign up top. Feels like unlocking a treasure, right?
- Choose 'New Repository' from the dropdown.
- Repo Details:
- Name your brainchild.
- Public or Private? Your call.
- Add a catchy description.
- Init with a README? Always a smart move.
- Pick a license if you're feeling it.
- Create It: Smash that 'Create repository' button.
- Bam! Repository Ready: Your new digital playground is set on GitHub.
Securing the Fort with a Token
- Settings, Please: Click your profile pic and hit 'Settings'.
- Developer Mode On: Find 'Developer settings' on the left.
- Token Time: Under 'Access Tokens', select 'Personal access tokens'.
- Token Generation:
- Click 'Generate token'. Feels like launching a rocket, huh?
- Name it something cool.
- Pick the powers (permissions) wisely.
- Expiry date? Your choice.
- Copy That Token: Guard it like a secret treasure.
Local Repo Clone: Bringing it Home
- Git Ready: No Git? Download it from the Git website.
- Terminal or Command Prompt: Open it. It's like opening the door to Narnia.
- Directory Navigation:
- Use 'cd' to move to your desired folder. Desktop? cd ~/Desktop.
- Clone Command:
- git clone <repository-url>
- Replace <repository-url> with yours.
- Token Authentication: Private repo? Use your token as the password.
- Cloned and Ready: Your repo's now on your local machine. Time to make magic!
Crafting Your CloudFormation Template.yaml
- New File in IDE: Click 'File' > 'New File'.
- Save with .yaml Extension: Name it like 'cfn-template.yaml'.
- Template Time: Paste your CloudFormation template here.
5. Template Validation: No Errors Allowed
- Save and Validate: Run cfn-lint -t <yourfile>.yaml in your terminal. To check your template for any syntax errors and provide feedback in the Output pane - keep it error-free.
6. Deployment File: Setting Up for Success
- New File Again: In your IDE, 'File' > 'New File'.
- Save as 'deployment-file.yaml'.
- Path and Tags: Include the file path of your CloudFormation template and any tags.
7. GitHub Actions: Keeping Your Code in Check
- Setup and establish the following folder structure: .github/workflows/pull-request.yaml.
- Define workflow to lint your pull requests.
8. Branching and Committing: Own Your Updates
· Create a new branch
· Add and commit your configs.
9. Git Sync Prereqs: Keep Your Stack in Sync
- AWS Console Login: Head over to the AWS Management Console.
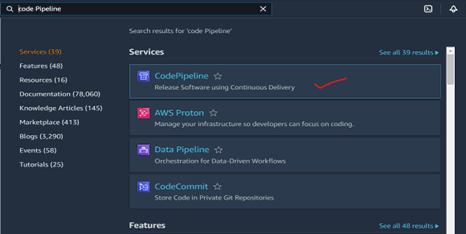
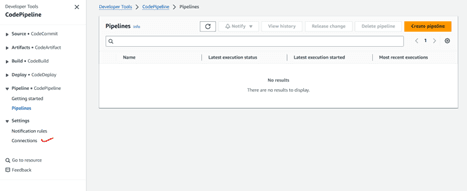
- Developer Tools Connection:
- Search ' Code Pipeline ' in AWS services.
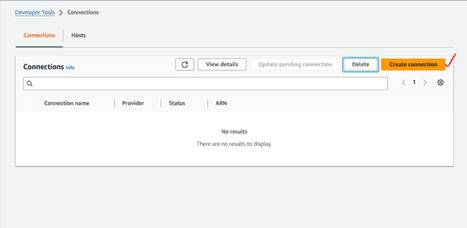
- Navigate to Connections
- Create a new connection to GitHub.
10. IAM Role Creation:
- Create the role that will deploy our CloudFormation template. Be sure to note the name you select for this as you’ll be using it to manage your stack later. This example uses gitsync-cloudformation-deployment-role.
- Navigate ' IAM ' in AWS services.
- Navigate to Connections
- Create a new role for Cloudformaton. (gitsync-demo-role)
- Create an inline policy for the role. (gitsync-demorole-policy)
11. Link up with CloudFormation!
Once the role has been created, you’ll create a new Stack:
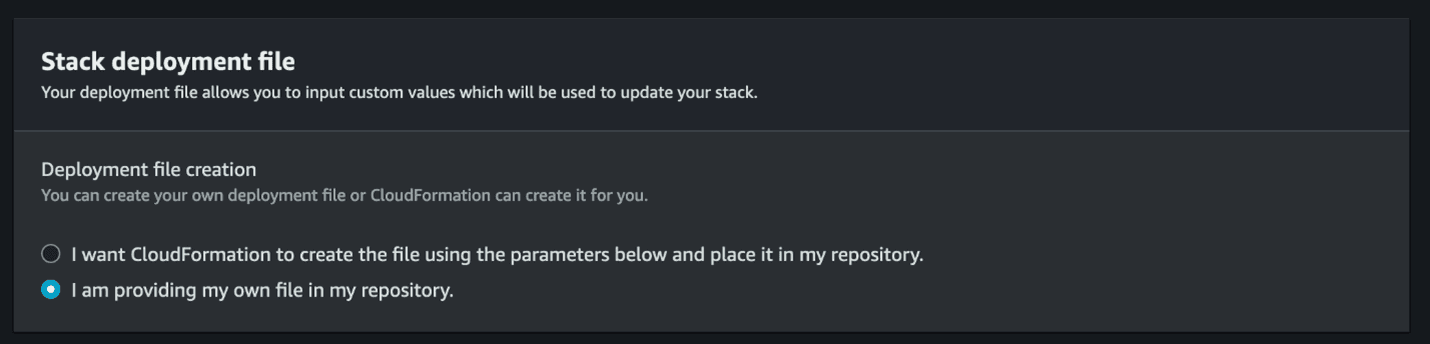
Here, you can see the new option to select Sync from Git template source, which you can configure on the next screen. Since you already created your stack deployment file, you can select I am providing my own file in my repository.
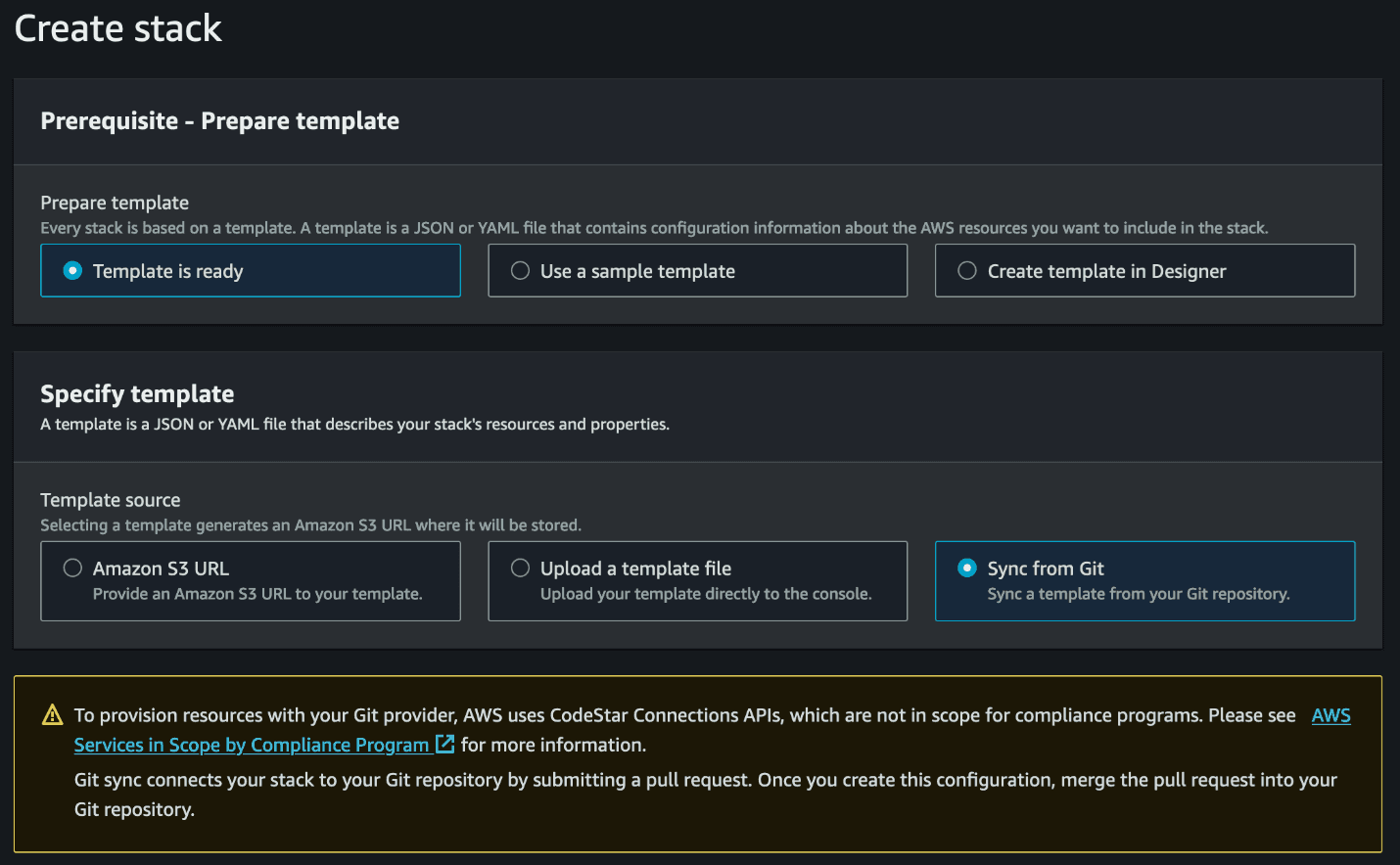
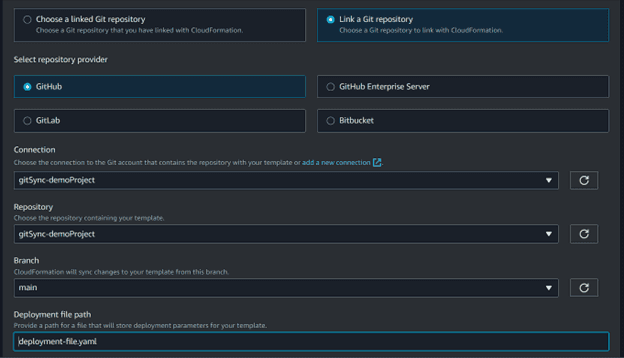
Next, you can configure your Git integration to choose your repository. Since it’s your first time, you’ll need to use the Connection you created beforehand and select your repository. Select GitHub, your connection, the repository, and branch, the deployment file location.
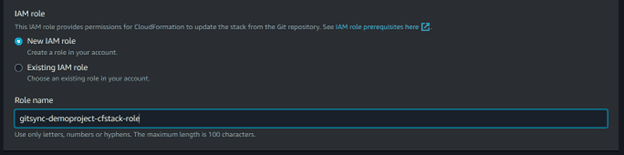
Now, you will select New IAM Role to create a service managed role. This role will enable Git sync to connect to your repository. You’ll only need to do this once; in the future you’ll be able to use the existing role you’ll create here.
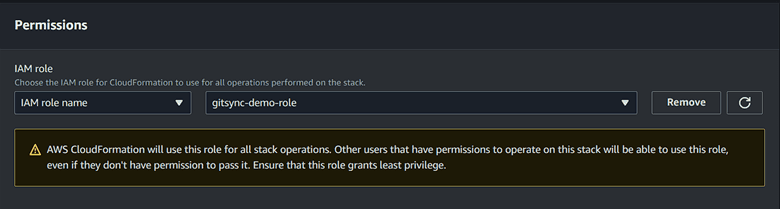
On the next page, you’ll select the IAM Role you created to manage this stack. This role controls the resources that CloudFormation will deploy. Stacks managed by Git sync must have a role already created.
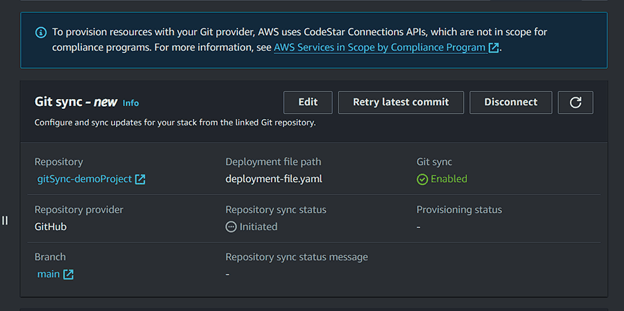
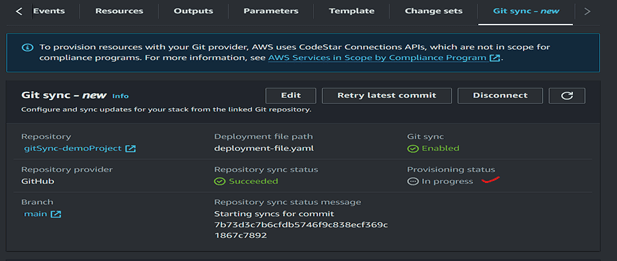
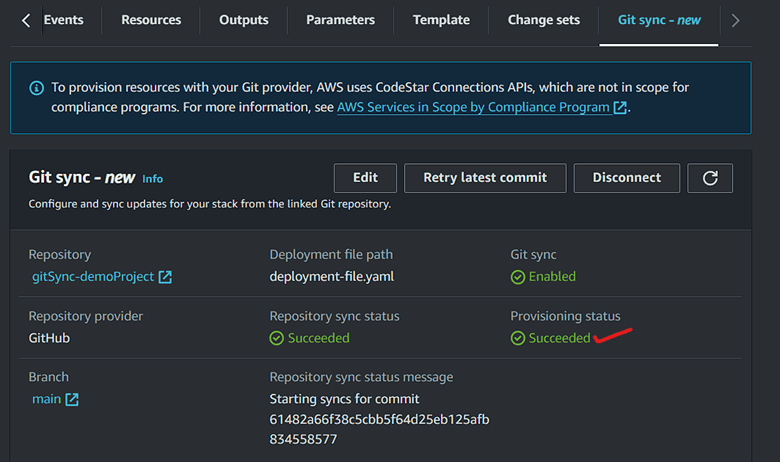
Finally, you can see the status of your sync in the new “Git sync” tab, including the configuration you provided earlier as well as the status of your sync, your previous deployments, and the option to retry or disconnect the sync if needed.
12. Give It a Whirl
- Get over to GitHub: log into your Github account.
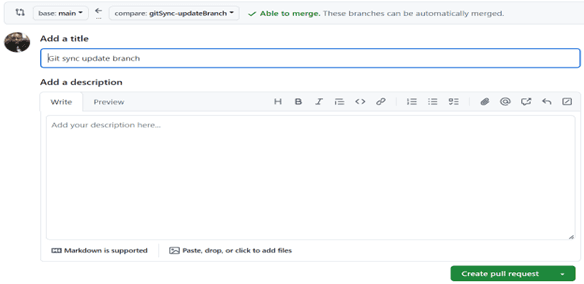
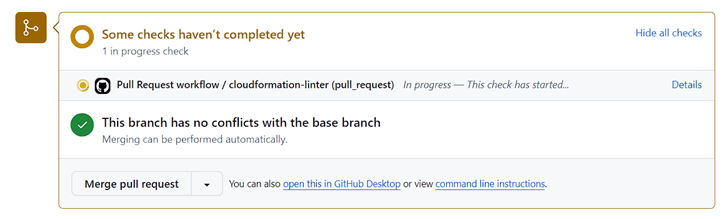
- Create a Pull Request: Create a new pull request and wait for lint checks to pass.
- Merge Pull Request: Include the file path of your CloudFormation template and any tags.
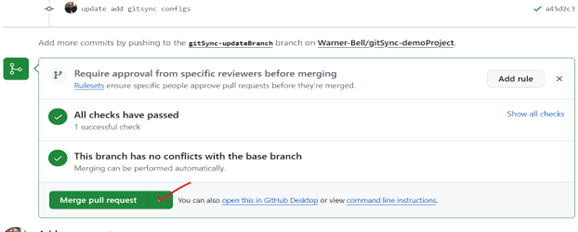
Return to the CloudFormation Console and see that the stack is being provisioned. You can also look at the stack details to see the events, outputs, etc.
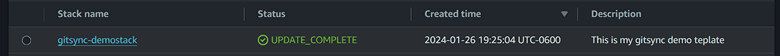
When the sync is complete Git sync will show the provisioning status as succeeded and the stack with all its resources will be deployed.
Conclusion: Wrapping Up Like a Pro
You've just set up a slick, automated environment for CloudFormation templates. Validation on pull requests and auto-deployment to your stack? Now when your repo/template is updated and merged gitsync will automatically make the changes to your cloudformation stack and resources. We got this! This is that next-level CI/CD for your infrastructure code, a brand new workflow for me, and as always Builder Fun!
