CloudCycle
Set lifecycle for your cloud resources to avoid surprising costs
Published May 26, 2024
I have recently forgot to Turn off / Terminate two ec2 instances running m5x.large and t3.medium that runs about 1 month and I just received a notification of my AWS monthly bill and shocked me!
At the first place I thought my account was hacked, But turns out that I just left two AWS EC2 Instances running. 🥲😔
So, that's why I came up with a basic solution and share it. So now, whether I forgot to turn it off / terminate a running AWS Resources, I don't have to worry about it anymore, if I have properly set the desired lifecycle of my cloud resources.
I have created a lambda function which get's executed every 15 minutes to check if the supported resources are due to termination or not.
Now, if you or your team forgot to terminate cloud resources, the CloudCycle will do the job for you.
- Golang - Since lambda function bills will be based on the duration of execution. At first, I developed this by using python and I have realized that I need to consider it's performance and execution time.
- Terraform - Used only for deployment and examples.
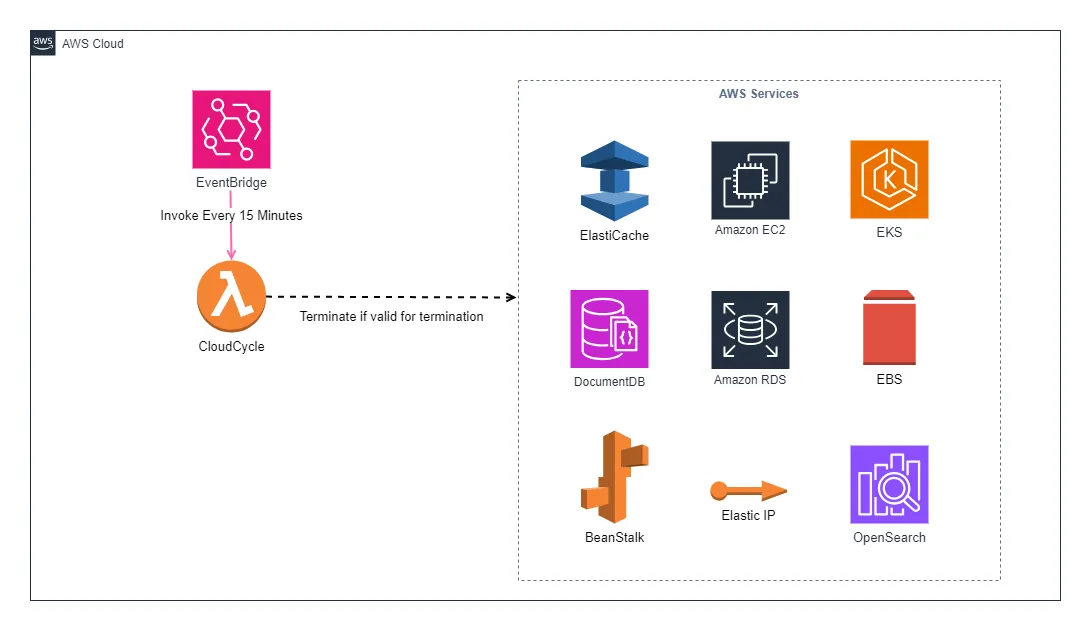
This setup will utilized the schedule expression of event bridge, In which event bridge get's executed every 15 minutes. In doing so, lambda function get validate if the supported resources is valid for termination.
But why termination? Instead of turning it off?
Of course there's a free tool available called Cloud-Custodian. But still, sometimes turning it off isn't enough and it can lead to lots of unused resources and can still occur minimal cost.
Below are the sample codes for EC2 Instance service.
My objective with CloudCycle is to automatically cleanup supported resources based on the specified duration or lifecycle through resource tagging, And to support the commonly used resources that causes AWS Bills to grow even though the cloud resources is not needed anymore.
No more story telling!
For complete documentation and project link, you can proceed directly to my GitHub repo below.
This repo is open for contributors!!! Some documents and cloud resources are currently WORK-IN-PROGRESS
Just specify that tag and set your desired lifecycle for supported resources with CloudCycle Key. Below are the supported duration.
| Suffixes | Detail | Sample Value |
|---|---|---|
m | Minutes | 60m |
h | Hours | 2h |
d | Days | 7d |
CloudCycle will get all the supported resources with a tagged key CloudCycle and it will simply compare the current time vs launch time of the supported resources with the specified
key/value pair resource tag if the supported resources are valid for termination.Below are the sample terraform code.
Specify ec2 lifecycle by 24 hours from it's launch date.
For deployment, you can refer to the github repo deployment page https://github.com/redopsbay/cloudcycle/blob/master/deploy/README.md
Sometimes it's better to let go than stay strong. Leaving up unused resources will incur costs.
And lastly, No nightmare's, No poverty! 😂🤣
