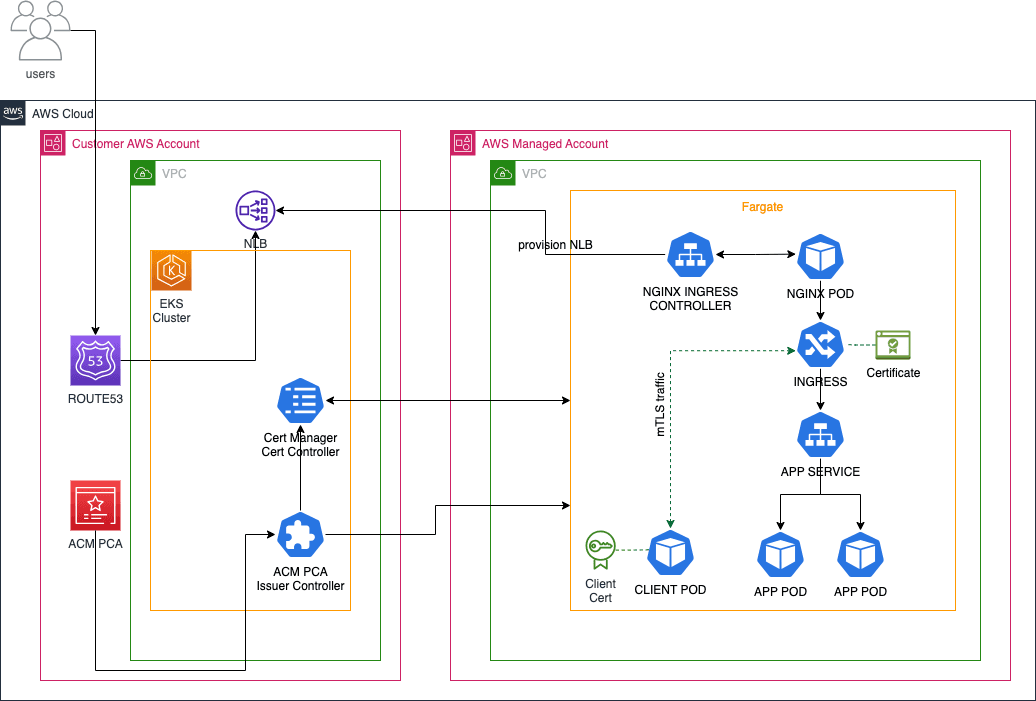
mTLS in Amazon EKS Fargate with NGINX Ingress Controller and ACM PCA
Ensure secure end-to-end communications between Kubernetes workloads
Step 2: Install and Configure the Cluster Components
Install ALB Controller on Fargate using Helm option
Download NGINX Ingress Controller manifest and customize it for Amazon EKS Fargate
Install Cert Manager with Helm
Install and Setup External DNS in the cluster (optional)
Step 3: Create Private Certificate Authority
Step 4: Install AWS-PCA-ISSUER
- Setting up NGINX Ingress Controller on Amazon EKS Fargate.
- Configuring mTLS with NGINX Ingress Controller using certificate issued by ACM Private CA.
- For mTLS support with NGINX Ingress controller behind a Service of
Type=LoadBalancer, you will need to create a TCP listener using a Network Load Balancer and implement mTLS on the target. - Privileged containers aren't supported on Fargate.
| About | |
|---|---|
| ✅ AWS experience | 200 - Intermediate |
| ⏱ Time to complete | 30 minutes |
| 🧩 Prerequisites | - AWS Account |
| 📢 Feedback | Any feedback, issues, or just a 👍 / 👎 ? |
| ⏰ Last Updated | 2024-01-19 |
- An active Amazon Web Services (AWS) account.
- Install the latest version of Helm CLI
- Install the latest version of AWS Command Line Interface (AWS CLI)
- Install the latest version of kubectl. To check your version, run:
kubectl version. - Install the latest version of eksctl. To check your version, run:
eksctl info. - A custom domain name to test the application.
- Ingress-Nginx Controller: It is an Ingress controller for Kubernetes using NGINX as a reverse proxy and load balancer. It can enable Client Certificate Authentication using additional annotations in Ingress Rule to achieve mTLS.
- AWS Certificate Manager Private CA: enables creation of private certificate authority (CA) hierarchies, including root and subordinate CAs, without the investment and maintenance costs of operating an on-premises CA.
- AWS Private CA Issuer: It is an addon to cert-manager that signs off certificate requests using AWS Private CA.
- AWS Load Balancer Controller: A Kubernetes controller to help manage Elastic Load Balancers for the Kubernetes cluster
- Cert-manager: is a Kubernetes add-on to automate the management and issuance of TLS certificates from various issuing sources.
- ExternalDNS: helps to automatically manage DNS routing of your applications using Amazon Route 53
- Sample Application Deployment: Deploy a sample workload for an mTLS-enabled service. This workload encompasses the deployment of a sample application configured for mutual TLS (mTLS) within a Kubernetes environment, with a specific focus on Amazon EKS.
There is a charge for operating a private CA. $400 per private CA per month for general-purpose mode and $50 per private CA per month for short-lived certificate mode. This charge is pro-rated for partial months based on when you create and delete the CA.
- Download the deploy.yaml template from https://kubernetes.github.io/ingress-nginx/deploy/#aws
- Edit the downloaded `deploy.yaml`` file to make the following changes:
nlb-ip as shown below:http-port=8080 and https-port=8081 as extra args to the deployment manifest as shown below:- Deploy the modified manifest
- Wait for about 60seconds for Fargate to schedule to ingress controller pod. Verify the installation with this command:
To setup ExternalDNS in your Kubernetes cluster, see Setting up ExternalDNS for services on AWS (on the GitHub website) and Set up ExternalDNS.
- Download sample
external-dnsmanifest
- Open the downloaded
external-dns.yamlfile and edit the--domain-filterflag to include your hosted zone(s). The following example is for a hosted zoneexample.com:
- Deploy the downloaded
external-dns.yamlfile
- Verify it deployed successfully.
- To create a private certificate authority, execute the content below in your terminal, replace example.com with your own value:
- Create and install your private CA certificate
- Issue the root certificate with the csr file from the previous step. Note that if you are using AWS CLI version 2, you will need to pass the CSR data through encoding prior to invoking the
issue-certificatecommand.
- Import the signed certificate as the root CA
- Import the root CA certificate to install it on the CA. AWS CLI version 2 needs passing the certificate data through encoding. Execute the command below:
- Inspect the status of the CA and confirm it is in active state. If it is active state, then it is ready for use
- Get the ARN of the CA:
Define your environment variables:
YOUR_PRIVATE_CA_ARN and example.com with your own values.The AWS PCA Issuer plugin works as an addon to the cert-manager that signs off certificate requests using AWS Certificate Manager Private Certificate Authority.
- Copy and paste the command below in your terminal to create a
pca-iam-policy.jsonfile:
- Create and IAM policy called
AWSPCAIssuerIAMPolicywith the command below:
- Create a Service Account for the AWS PCA Issuer plugin with the command below:
IAM_POLICY_ARN with the ARN value retrieved previously.- Add the AWS PCA Issuer Helm repository and run the helm install command:
- Verify that AWS PCA issuer is configured correctly by running following command after about 60 seconds:
- Copy and paste the command below in your terminal to create the Cluster Issuer and Certificates files:
- Copy and paste the command below in your terminal to create
mtls-cert.yamlfile. The file will create a secret containing CA certificate along with the Server Certificate that can be used for both TLS and Client Auth. It will also create an additional secret that will be used by the client application or you can create just one certificate use the same secret.
- Create an issuer in Amazon EKS Cluster and generate TLS certificates for the backend applications
- Copy and paste the command below in your terminal to create an example workload:
- Run the commands below to create the workload:
- Copy and paste the command below in your terminal to create an Ingress manifest file
ingress.yamlfor the workload:
- Copy and paste the command below in your terminal to create a test client pod that has the necessary client certificate to interact with the application:
- Let’s verify if we can access the application from the test pod. Exec into the pod:
- Run a curl command to test connectivity to the application
- Let’s enable mTLS in the ingress manifest
ingress.yamlwe previously created. Uncomment the annotations below in theingress.yamlas shown below:
- Verify that the test pod is able to connect with the application using a mutual certificate key file. Exec into the pod:
- Run a curl command to test connectivity to the application
Any opinions in this post are those of the individual author and may not reflect the opinions of AWS.
